Valkyrie Verdict Network Sensor
One of the key benefits of Valkyrie Verdict is its ability to give a trusted verdict within 45 seconds on 92% of files (after automated analysis), and 4 hours on the remaining 8% (after human analysis). Our industry leading auto-analysis consists of several static and dynamic techniques, including state-of-the-art machine learning, precise detectors and dynamic behavior signatures.
Nevertheless, it is impossible to provide 100% threat visibility using automated techniques alone as many problems in malware analysis have been shown to be undecidable [1, 2]. Many of these results are based on the fact that precisely deciding whether a given program/input satisfies a certain post-condition, for an arbitrary post-condition, is undecidable. The proofs are based on two general techniques:
* Either they build a self-contradictory program assuming the existence of a decider for the given problem, similar to [3]
* They give a reduction from a well-known undecidable problem, such as the Halting Problem, similar to [4]
The 8% of unclassified files that require further testing are then analyzed by human experts who specialize in identifying complex and zero-day malware samples. Verdicts on these files are available to our users after 4-hours according to our SLA. Valkyrie customers can be confident that 100% of threats have been correctly identified after this 4 hour period. This isn’t some wild marketing claim - it is a scientific ‘100%’ built on the candid recognition that even the most advanced automatic tests available today cannot provide the correct verdict on all files. For those that remain, human analysis is absolutely essential. Users should always beware vendors that claim total protection based on automated mechanisms alone.
Customers who also use Comodo security solutions on their network are, of course, completely safe during this four-hour period. The 8% of unknown files will be isolated in a secure virtual container which cannot access other processes, system files or user data.
Valkyrie Verdict Sensor listens incoming traffic in to your network and extracts executable files. First it queries extracted file from Valkyrie Verdict Cloud API and if verdict is not available, uploads the file to analyze. Sensor currently in Beta version and supports only HTTP protocol.
Sensor Package Information:
valkyrie_verdict_network_sensor.tar.gz
Archive SHA-256: d0fdf748e878db9caa217365321a37b7976d5882eb71c9a0a929c7841d06738e
Prerequisites
Operating System:
Description: Ubuntu 16.04.3 LTS
Release: 16.04
Codename: xenial
-
Active Valkyrie Verdict User (Register via https://verdict.valkyrie.comodo.com/)
Installation
-
Extract verdict sensor archive file
$ tar -xvf valkyrie_verdict_network_sensor.tar.gz
-
Go to verdict sensor directory
$ cd valkyrie_verdict_network_sensor
-
Execute installation script (with sudo)
$ sudo ./install.sh
Installation starts and to finalize configuration for your OS, you should provide following information:
-
Installation script shall ask:
Enter Valkyrie-Verdict API Key:
Please enter your Valkyrie Verdict API Key, you could get your API key from:
-
Installation script shall ask:
Enter network interface adapter name:
Please enter your primary network interface name (like: etho, eno1, etc.).
Note: you could get your network interface name using:
$ netstat -i
Installation script shall finish afterwards.
-
-
Check Valkyrie Verdict Network Sensor service is running:
$ systemctl status valkyrie_network_sensor
You should see service is running, like following:
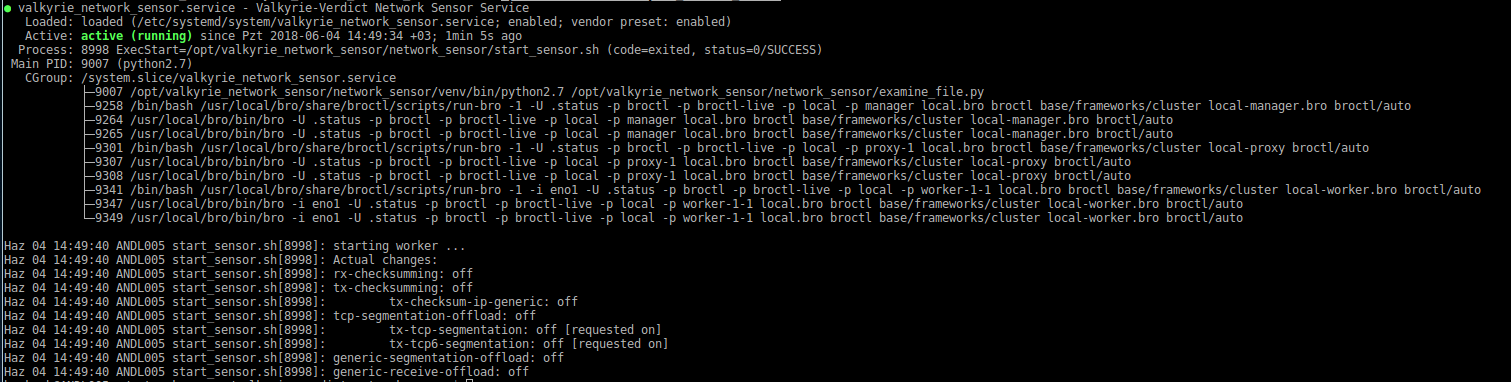
-
Check Log file
Check following log file, whether it has error or not:
$ /var/log/valkyrie_network_sensor/network_sensor.log
-
Test Sensor
-
Download an executable file using HTTP protocol
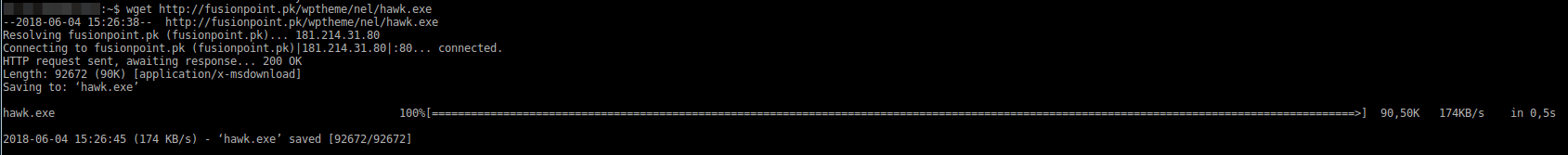
-
Check that sensor extract the file and query / upload using Valkyrie Verdict
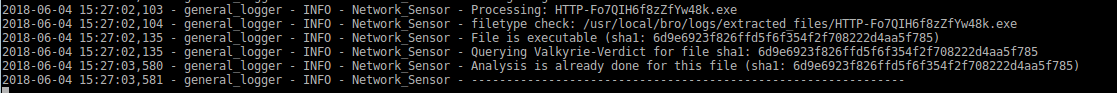
-
Check that file is listed in User's dashboard (see file's SHA1 in 'Last 10 Queried Files' list)

-
[1] Ali A. Selçuk, Fatih Orhan, Berker Batur, "Undecidable Problems in Malware Analysis", 12th International Conference for Internet Technology and Secured Transactions (ICITST), 2017.
Online version: https://comodemia.comodo.com/Undecidable_Problems_in_Malware_Analysis.pdf
[2] David Evans, "On the Impossibility of Virus Detection", 2017.
Online version: https://enterprise.comodo.com/whitepaper/Impossibility_of_Virus_Detection_WP.pdf
[3] Fred Cohen, “Computer viruses: theory and experiments”, Computers and Security, 6(1):22-35, 1987
[4] Fred Cohen, “Computational aspects of computer viruses”, Computers and Security, 8(4):325-344, 1989.
